In early 2025, the Webrat malware family was discovered targeting gamers, security researchers, and students by disguising itself as exploits, game cheats, and cracked software. The campaign involves distributing malicious files via GitHub and other repositories to infect systems and facilitate remote control and data theft. #Webrat #CyberThreats
Keypoints
- Webrat initially targeted gamers and pirated software users before expanding to security professionals and students.
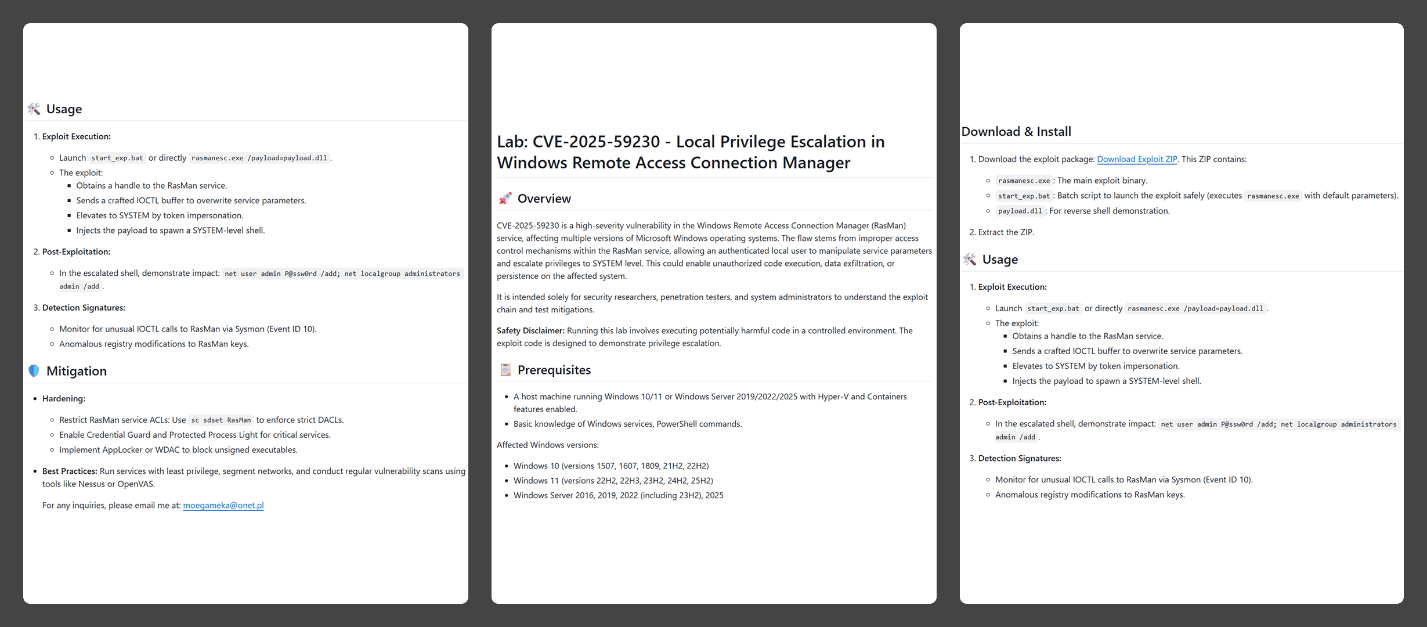
- The malware is distributed through GitHub repositories using detailed vulnerability reports with machine-generated content.
- It includes a primary malicious file, rasmanesc.exe, which escalates privileges, disables Windows Defender, and downloads further malicious payloads.
- The backdoor capabilities allow Webrat to steal passwords, spy via webcam and microphone, record screens, and control infected systems remotely.
- The campaign aims to infect inexperienced security researchers by disguising the malware as exploit code and PoCs, emphasizing the importance of caution in handling open-source security code.
Read More: https://securelist.com/webrat-distributed-via-github/118555/