A legitimate open-source tool called Nezha is being exploited by hackers to gain full control over computers through a Remote Access Trojan (RAT). Experts warn that Nezha’s widespread use and ease of deployment make it a significant threat, especially when used to evade detection and maintain persistence. #Nezha #RemoteAccessTrojan
Keypoints
- Nezha was originally designed as a server health monitoring tool with nearly 10,000 GitHub stars.
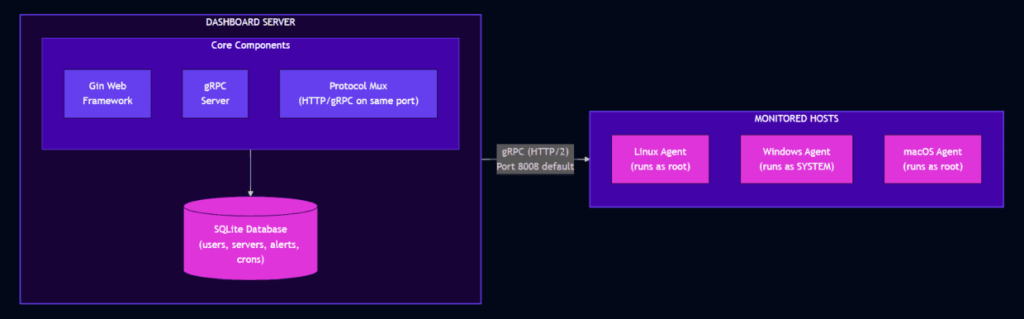
- Hackers repurpose Nezha as a full-featured Remote Access Trojan that provides SYSTEM/root level access.
- Nezha works across multiple platforms, including Windows, Linux, macOS, and routers, enabling control of many devices from a single dashboard.
- The tool’s traffic appears normal, making it difficult to detect malicious activity without inspection.
- Security experts recommend proactive detection of Nezha and emphasize the importance of a layered “Defense in Depth” security strategy.
Read More: https://hackread.com/hackers-abuse-monitoring-tool-nezha-trojan/