This article details a phishing attack involving a malicious PDF that leads to a fake login page designed to steal business credentials. It emphasizes the importance of vigilance and proper cybersecurity tools to prevent such intrusions. #Ionoscloud #Phishing #TelegramHack
Keypoints
- The malicious PDF mimics a purchase order and contains a suspicious link leading to a fake login webpage.
- The phishing site harvests credentials and sends them to the attacker’s Telegram account along with device details.
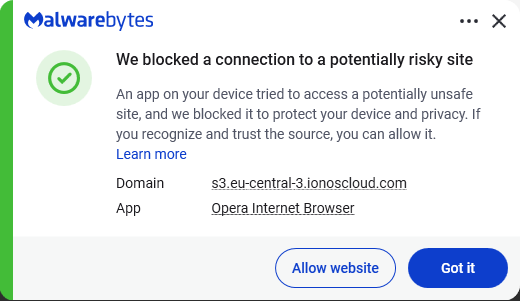
- Attackers use reputable cloud services like IONOS Cloud to host their phishing sites, making detection more difficult.
- The JavaScript used in the attack is heavily obfuscated but can be analyzed to understand the data collection process.
- Preventative measures include verifying email attachments, using anti-malware solutions, and employing password managers.
Read More: https://www.malwarebytes.com/blog/threat-intel/2025/12/inside-a-purchase-order-pdf-phishing-campaign