Researchers have uncovered a malicious campaign targeting EU IT workers, delivering fake GitHub Desktop installers via sophisticated malvertising tactics. The campaign leverages GPU-based decryption and evasion techniques to evade detection and enables potential credential theft and lateral movement. #GPUGate #AtomicStealer
Keypoints
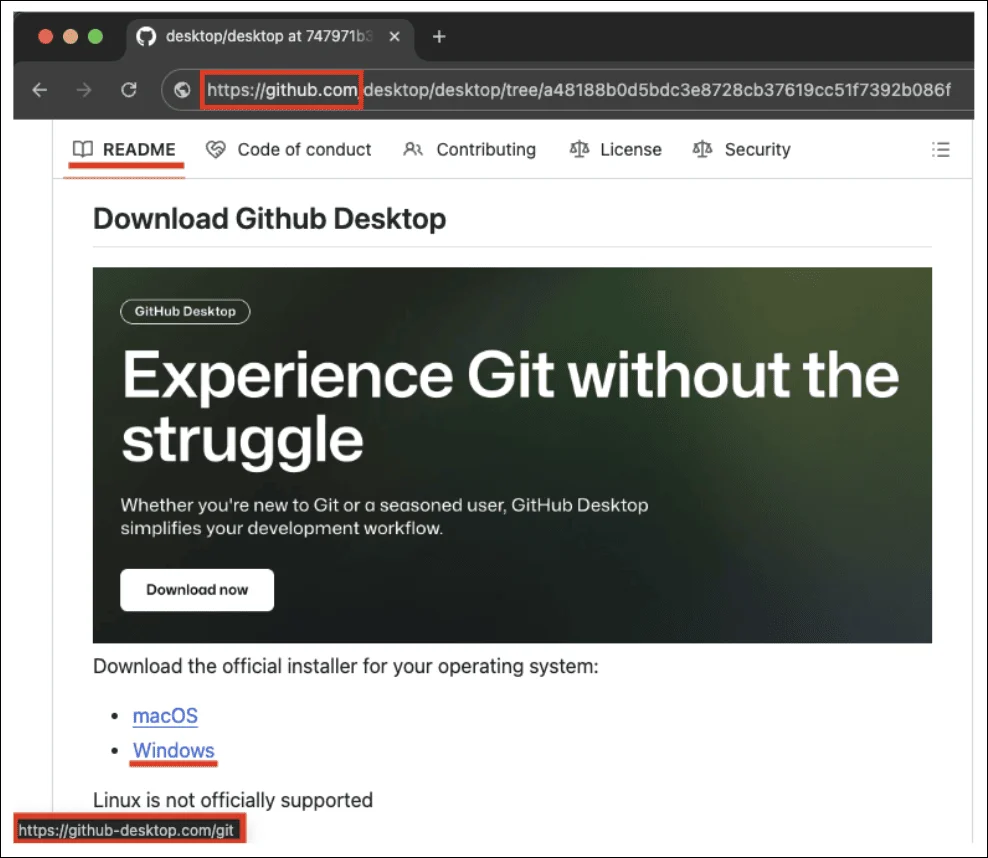
- The campaign uses malicious Google Ads to direct users to fake GitHub Desktop download pages.
- Download links lead to lookalike domains serving malware tailored for MacOS and Windows systems.
- The Windows malware includes dummy files and advanced tactics to evade antivirus detection.
- The payload gains persistence through scheduled tasks, registry modifications, and privilege escalation.
- The campaign primarily targets IT professionals within the EU to facilitate deeper network infiltration.
Read More: https://www.helpnetsecurity.com/2025/09/09/github-desktop-malvertising-it-workers/