Ransomware groups are increasingly exploiting Remote Monitoring and Management (RMM) tools for stealthy cyberattacks, blending legitimate IT functions with malicious activities. These tactics pose significant detection challenges and highlight the importance of enhanced security measures. #Ransomware #RMMexploitation
Keypoints
- Cybercriminal gangs are leveraging RMM tools like AnyDesk and ScreenConnect for persistent network access.
- The use of legitimate management tools allows attackers to evade traditional security controls and perform lateral movements.
- Incidents in 2024-2025 involved multi-tool exploits by groups such as Hunters International and Medusa targeting organizations in the US and UK.
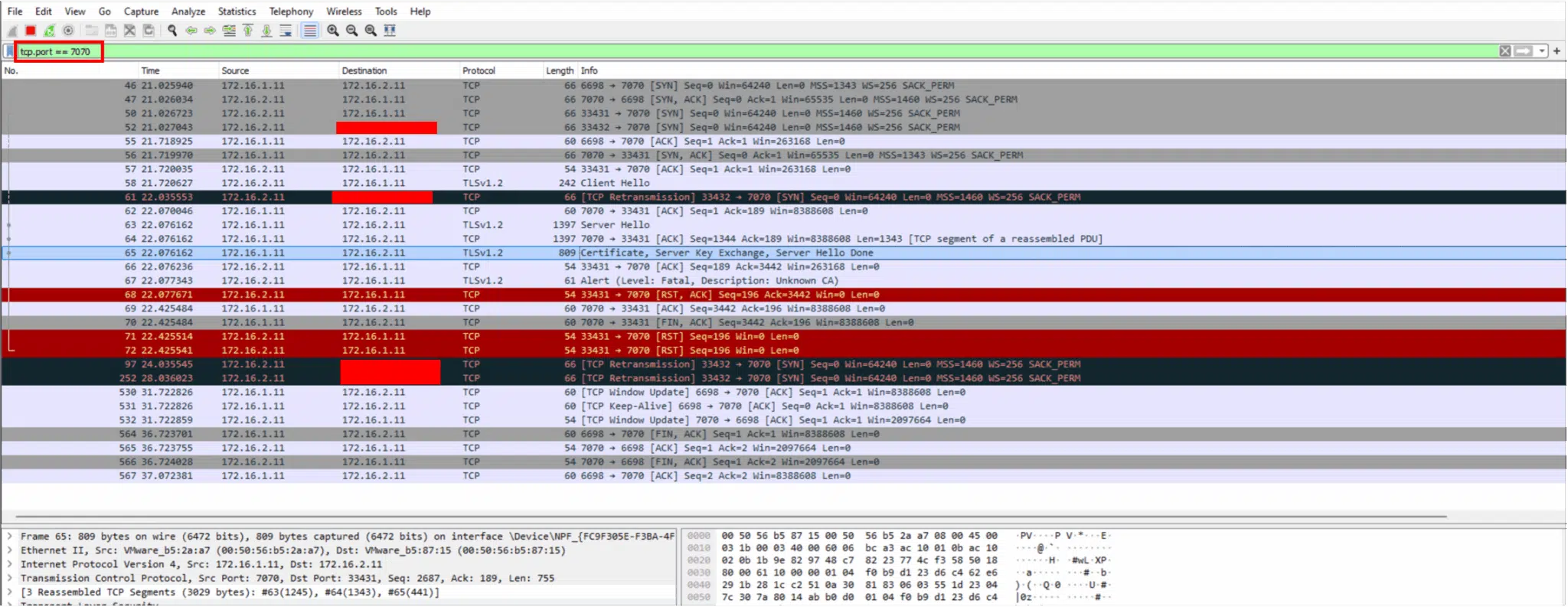
- Network analysis detected suspicious activity, including unusual traffic on ports used by RMM tools, prompting automated alerts.
- Measures such as strict controls, multi-factor authentication, and regular audits are critical to mitigate RMM-based cyber threats.
Read More: https://gbhackers.com/ransomware-groups-weaponize-rmm-tools/