Cybercriminals are increasingly abusing legitimate software installer frameworks like Inno Setup to distribute malware covertly. This tactic involves sophisticated multi-stage infection chains that evade detection, highlighting the importance of vigilant security measures. #InnoSetup #RedLineStealer
Keypoints
- Cybercriminals exploit Inno Setup’s trusted reputation to deliver malicious payloads.
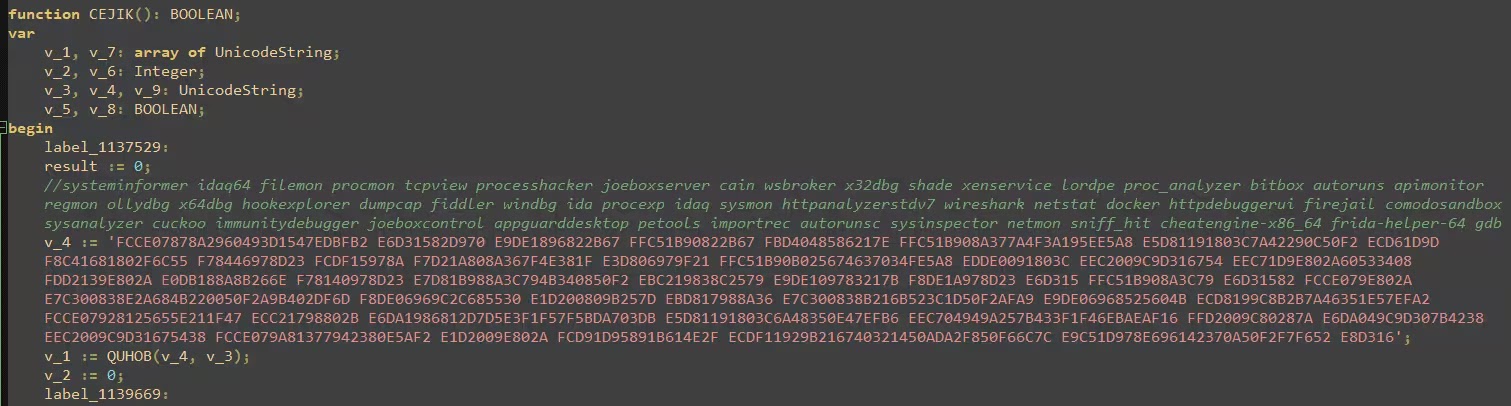
- The malware delivery involves multi-stage processes, including shellcode execution and hijackLoader deployment.
- Attackers use obfuscation techniques such as XOR encryption and environment checks to evade detection.
- Payloads like RedLine Stealer steal sensitive data and employ obfuscation tactics to hinder analysis.
- Organizations should implement robust monitoring to detect indicators like unsigned DLLs and suspicious scheduled tasks.
Read More: https://gbhackers.com/hackers-abuse-legitimate-inno-setup-installer/