Microsoft has released security updates for Windows 10 and Windows 11 that address multiple critical vulnerabilities, including privilege escalation, remote code execution, and spoofing issues. These patches resolve actively exploited flaws reported by threat intelligence teams, enhancing the security posture of Windows operating systems. #Windows10 #Windows11
Keypoints
- Security updates fix 17 privilege escalation, 2 security feature bypass, 28 remote code execution, 15 information disclosure, 7 denial of service, and 2 spoofing vulnerabilities in Windows 10 and 11.
- Several actively exploited privilege escalation vulnerabilities were discovered by Microsoft Threat Intelligence Center, Google Threat Intelligence Group, and external researchers.
- CVE-2025-30400 and CVE-2025-32701 are notable privilege escalation flaws in the Desktop Window Manager (DWM) and Common Log File System Driver that allow local attackers to gain SYSTEM privileges.
- A remote code execution vulnerability in the Microsoft Scripting Engine (CVE-2025-30397) can be exploited via specially crafted links in Microsoft Edge or Internet Explorer.
- A spoofing vulnerability in Microsoft Defender for Identity (CVE-2025-26685) lets unauthenticated attackers spoof accounts over adjacent networks.
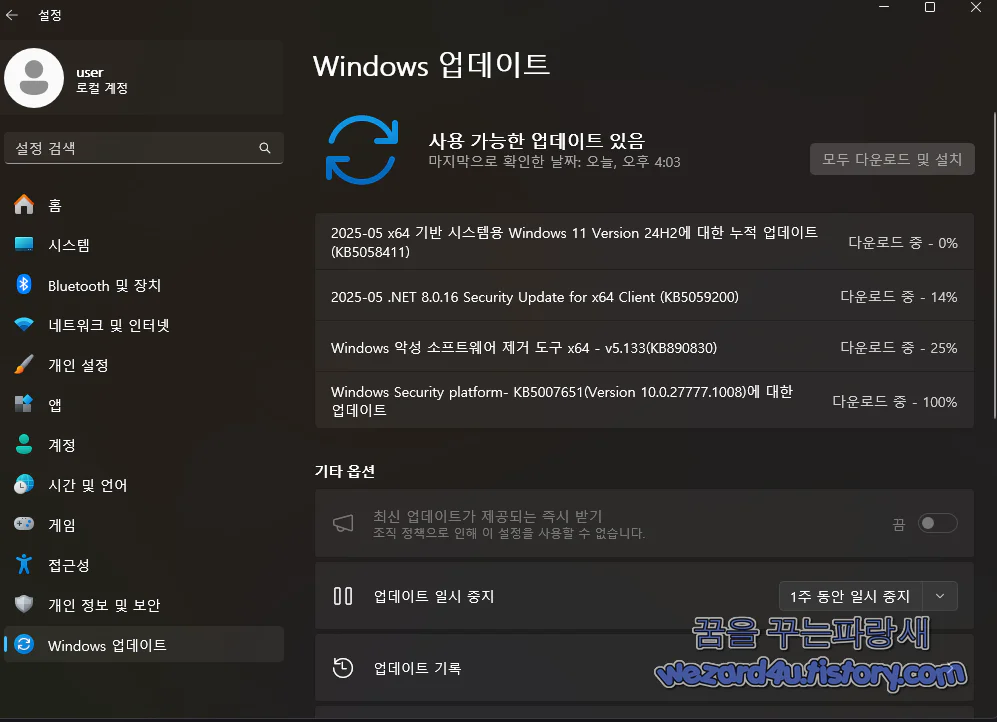
- Windows 10 version 22H2 and Windows 11 versions 22H2, 23H2, and 24H2 received additional security fixes and feature improvements, including updates to Copilot+ PC and AI-powered Windows search capabilities.
- Users are strongly advised to apply these cumulative updates promptly to mitigate existing security risks and maintain system safety.
MITRE Techniques
- [T1548] Abuse Elevation Control Mechanism – Exploiting Windows DWM Core Library and Common Log File System Driver to escalate privileges locally (“after release of Windows DWM, a privileged attacker can elevate privileges locally”).
- [T1203] Exploitation for Client Execution – Using Microsoft Scripting Engine vulnerability to execute code remotely via specially crafted links in browsers (“an attacker can trick an authenticated user to click a specially crafted link”).
- [T1110] Brute Force / Account Manipulation – Spoofing accounts through a flaw in Microsoft Defender for Identity due to improper authentication (“an unauthenticated attacker can spoof accounts over adjacent networks”).
- [T1059] Command and Scripting Interpreter – Command injection in Visual Studio due to improper sanitization allows local code execution (“special elements in commands are improperly neutralized, allowing local code execution”).
Indicators of Compromise
- [CVE Identifiers] Relevant CVE numbers for vulnerabilities – CVE-2025-30400, CVE-2025-32701, CVE-2025-30397, CVE-2025-26685, CVE-2025-32702, and others mentioned indicating specific security issues.
- [File Names] Vulnerable system components – Desktop Window Manager (DWM), Common Log File System Driver, Windows Scripting Engine, Microsoft Defender for Identity, Visual Studio ancillary function driver.
Read more: https://wezard4u.tistory.com/429486