Broadcom has identified three critical vulnerabilities in VMware ESXi affecting local admin privileges, enabling code execution on the host and memory leakage. The vulnerabilities are actively exploited, posing severe risks to various VMware products, necessitating immediate updates. Affected: VMware ESXi, VMware Workstation, VMware Fusion, VMware Cloud Foundation, VMware Telco Cloud Platform
Keypoints :
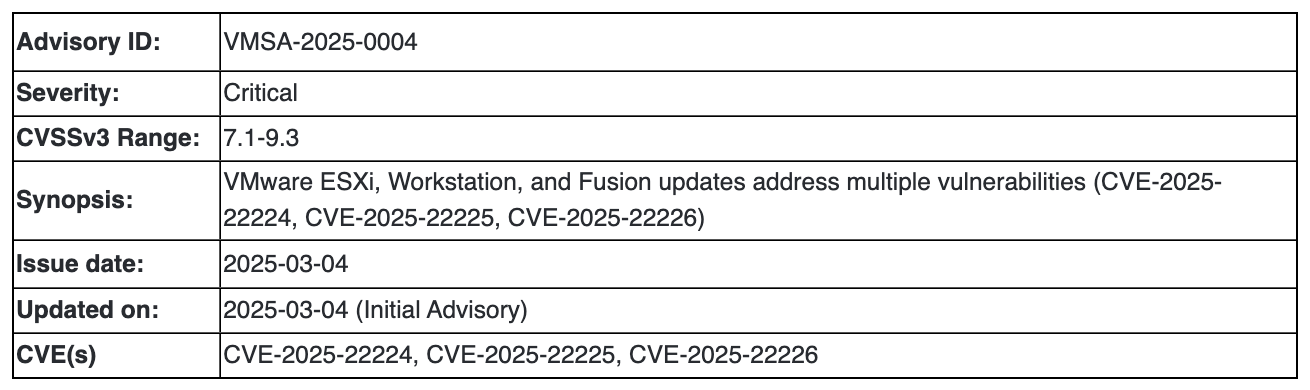
- Three critical zero-day vulnerabilities disclosed by Broadcom on March 4, 2025.
- Vulnerabilities identified as CVE-2025-22224, CVE-2025-22225, and CVE-2025-22226.
- CVE-2025-22224 is rated 9.3 on the CVSSv3 scale, representing the highest severity.
- Exploited by attackers with local administrative access on a virtual machine.
- Potential for hypervisor-level code execution and broader system compromise.
- Vulnerabilities impact multiple VMware products, including ESXi and Workstation.
- Patch updates have been released for affected products with no available workarounds.
- Exploitation confirmed in real-world attacks documented by the Microsoft Threat Intelligence Center.
- Users are urged to update to the latest software versions to mitigate risk.
MITRE Techniques :
- TA0002: Execution – exploit vulnerabilities to execute malicious code on the host system.
- TA0003: Persistence – leverage access to maintain a foothold on compromised virtual machines.
- TA0004: Privilege Escalation – exploit CVE-2025-22225 to gain higher privileges on the host OS.
- TA0007: Discovery – use CVE-2025-22226 to leak sensitive information such as encryption keys from memory.
Indicator of Compromise :
- [CVE] CVE-2025-22224
- [CVE] CVE-2025-22225
- [CVE] CVE-2025-22226
Full Story: https://gridinsoft.com/blogs/vmware-esxi-vulnerabilities-exploited/