Summary: A critical vulnerability, CVE-2024-22036, has been identified in Rancher environments, allowing remote code execution (RCE) due to excessive permissions granted to node drivers. This flaw poses significant risks, particularly in production and development setups, enabling attackers to gain root access and potentially compromise entire infrastructures.
Threat Actor: Unknown | unknown
Victim: SUSE Rancher | SUSE Rancher
Key Point :
- CVE-2024-22036 has a CVSS score of 9.1, indicating a severe risk of RCE in Rancher environments.
- Attackers can exploit path manipulation, inadequate ownership of critical binaries, and symbolic links to escalate privileges.
- Patches are available in versions 2.7.16, 2.8.9, and 2.9.3, which tighten permissions and restrict driver functionality.
- Workarounds include limiting driver execution to trusted sources and restricting admin privileges to mitigate risks.
A new vulnerability, CVE-2024-22036, has been disclosed by the SUSE Rancher Security team, highlighting a critical flaw that enables remote code execution (RCE) in Rancher environments. Rated 9.1 on the CVSS scale, this vulnerability presents a significant risk, allowing attackers to exploit cluster and node drivers to escape the chroot jail and gain root access within the Rancher container.
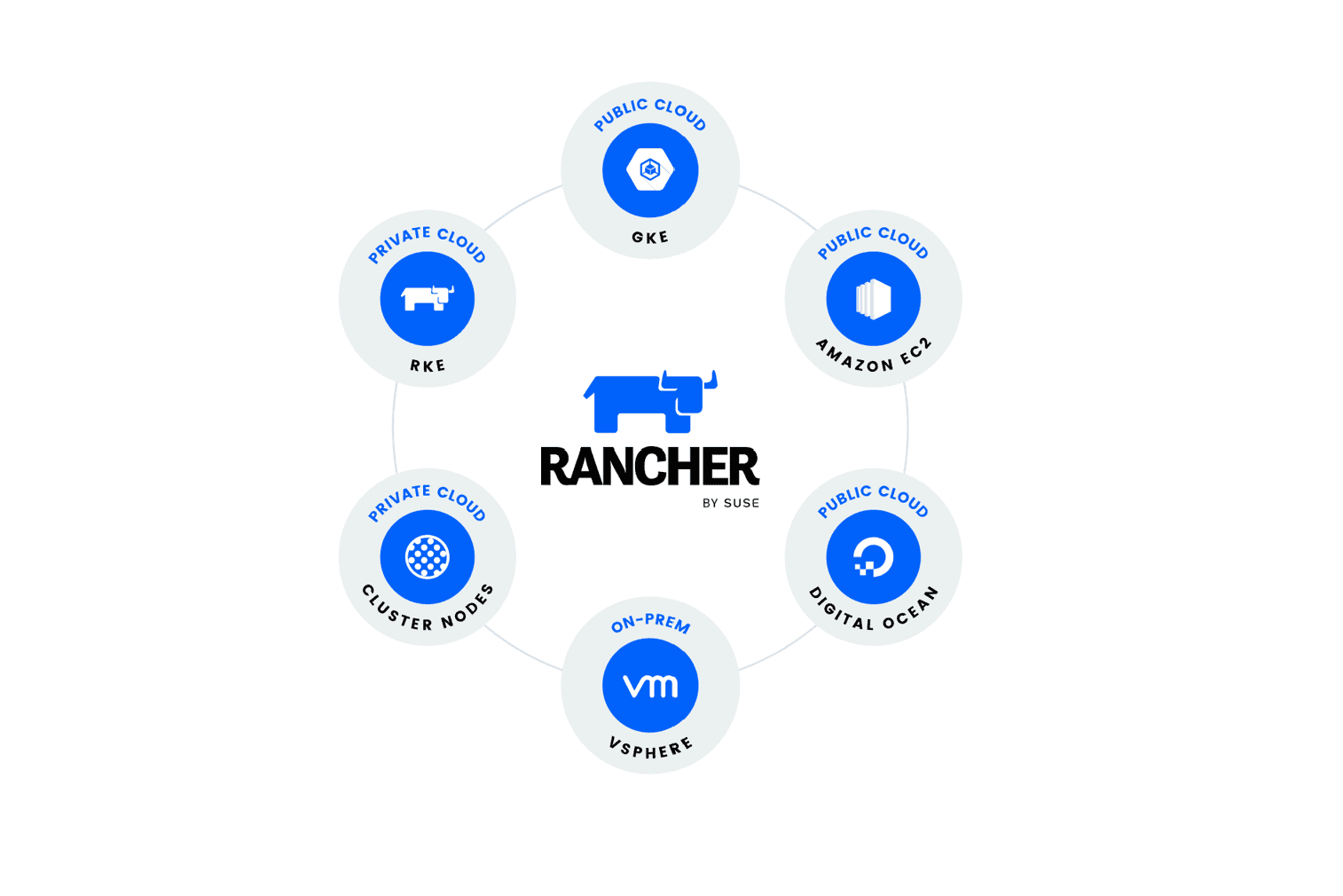
Rancher, a leading open-source container management platform, is widely used in enterprise environments to streamline Kubernetes deployments. This vulnerability directly affects Rancher’s internal mechanisms for managing node drivers, which typically execute with restricted permissions in a “jail” environment. However, the SUSE advisory notes that “the drivers are executed with excessive permissions,” making it possible for attackers to manipulate these drivers for privilege escalation.
Attackers could leverage the following aspects of the vulnerability:
- Path Manipulation: During startup, Rancher adds
/opt/drivers/management-state/binto the PATH environment variable, increasing the attack surface for malicious drivers. - Inadequate Ownership: Critical binaries such as
/usr/bin/rancher-machine,/usr/bin/helm_v3, and/usr/bin/kustomizeare assigned to UID 1001 and GID 127, rather than root, allowing attackers to potentially exploit these files. - Symbolic Links: The lack of file type validation permits symbolic links, enabling attackers to inject malicious drivers by registering these links within the system.
The security advisory warns that “further privilege escalation is possible based on living off the land within the Rancher container itself,” with even greater risks in development and test setups that use privileged Docker containers.
In production settings, attackers could gain root access to the Rancher container and potentially escalate privileges by exploiting tools and configurations within the container. In testing and development environments running with a privileged Docker setup, attackers can escape the container entirely, gaining access to the host system—a serious escalation that compromises the entire infrastructure.
SUSE Rancher has released patches in versions 2.7.16, 2.8.9, and 2.9.3, which address this vulnerability by tightening permission levels and restricting driver functionality. Users are strongly urged to “use trusted drivers only” to mitigate the risk of malicious drivers bypassing security controls.
For those unable to upgrade immediately, the advisory recommends two key workarounds:
- Limit Driver Execution to Trusted Sources: Restricting drivers to vetted, trusted sources minimizes the risk of malicious exploitation.
- Restrict Admin Privileges: Access should be limited to trusted users only for both Admins and Restricted Admins to reduce potential vectors for unauthorized access.