Summary: The APT33 Iranian hacking group has deployed new Tickler malware to infiltrate networks in various sectors, including government and defense, as part of an intelligence collection campaign. Microsoft has identified their use of compromised Azure infrastructure for command-and-control operations and has implemented mandatory multi-factor authentication to enhance security against such threats.
Threat Actor: APT33 | APT33
Victim: Various organizations in government, defense, and education sectors | Various organizations
Key Point :
- APT33 utilized Tickler malware to backdoor networks in the U.S. and UAE between April and July 2024.
- The group conducted password spray attacks to gain access to compromised accounts, particularly in the education sector.
- Microsoft disrupted the fraudulent Azure subscriptions used by APT33 for command-and-control operations.
- Mandatory multi-factor authentication (MFA) for Azure accounts will be enforced starting October 15, 2024, to mitigate risks from such attacks.

The APT33 Iranian hacking group has used new Tickler malware to backdoor the networks of organizations in the government, defense, satellite, oil and gas sectors in the United States and the United Arab Emirates.
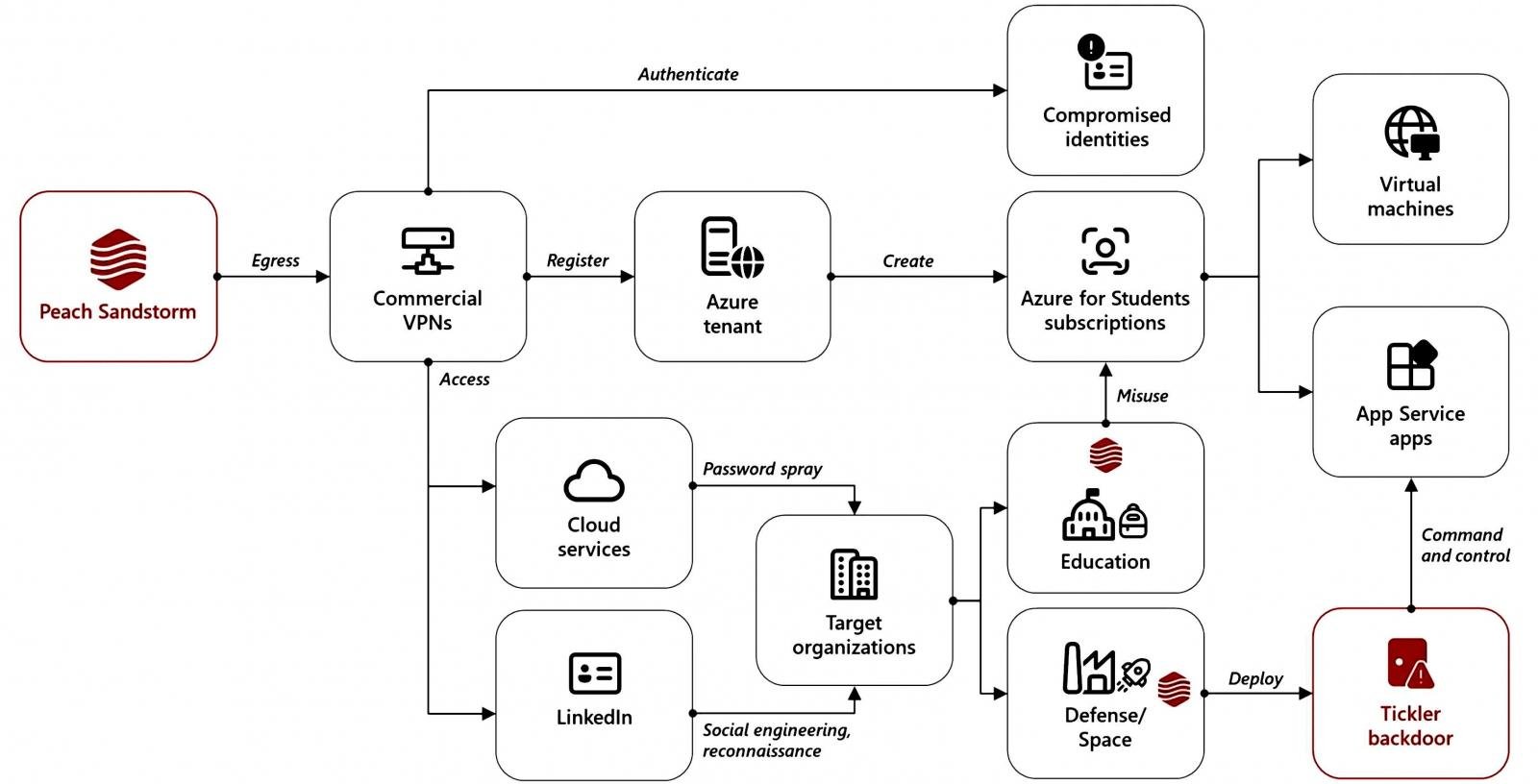
As Microsoft security researchers observed, the threat group (also tracked as Peach Sandstorm and Refined Kitten), which operates on behalf of the Iranian Islamic Revolutionary Guard Corps (IRGC), used this new malware as part of an intelligence collection campaign between April and July 2024.
Throughout these attacks, the threat actors leveraged Microsoft Azure infrastructure for command-and-control (C2), using fraudulent, attacker-controlled Azure subscriptions that the company has since disrupted.
APT33 breached targeted organizations in the defense, space, education, and government sectors following successful password spray attacks between April and May 2024. In these attacks, they attempted to gain access to many accounts using a small number of commonly used passwords to avoid triggering account lockouts.
“While the password spray activity appeared consistently across sectors, Microsoft observed Peach Sandstorm exclusively leveraging compromised user accounts in the education sector to procure operational infrastructure. In these cases, the threat actor accessed existing Azure subscriptions or created one using the compromised account to host their infrastructure,” Microsoft said.
The Azure infrastructure they gained control of was used in subsequent operations targeting the government, defense, and space sectors.
“In the past year, Peach Sandstorm has successfully compromised several organizations, primarily in the aforementioned sectors, using bespoke tooling,” Microsoft added.
The Iranian threat group also used this tactic in November 2023 to compromise the networks of defense contractors worldwide and deploy FalseFont backdoor malware.
In September, Microsoft warned of another APT33 campaign that had targeted thousands of organizations worldwide in extensive password spray attacks since February 2023, leading to breaches in the defense, satellite, and pharmaceutical sectors.
Microsoft has announced that starting October 15, multi-factor authentication (MFA) will be mandatory for all Azure sign-in attempts to protect Azure accounts against phishing and hijacking attempts.
The company has previously found that MFA allows 99.99% of MFA-enabled accounts to resist hacking attempts and reduces the risk of compromise by 98.56%, even when attackers attempt to breach accounts using previously compromised credentials.