A North Korean threat actor, APT37, delivered a backdoor called BirdCall embedded in popular Android card games from Sqgame to target ethnic Koreans in the Yanbian region, enabling screenshots, call recording, and broad data theft. ESET discovered seven Android versions of BirdCall and traced the infection to a compromised update package on Sqgame’s site, a campaign likely aimed at North Korean refugees and defectors. #BirdCall #APT37 #Sqgame #Yanbian #ESET
Keypoints
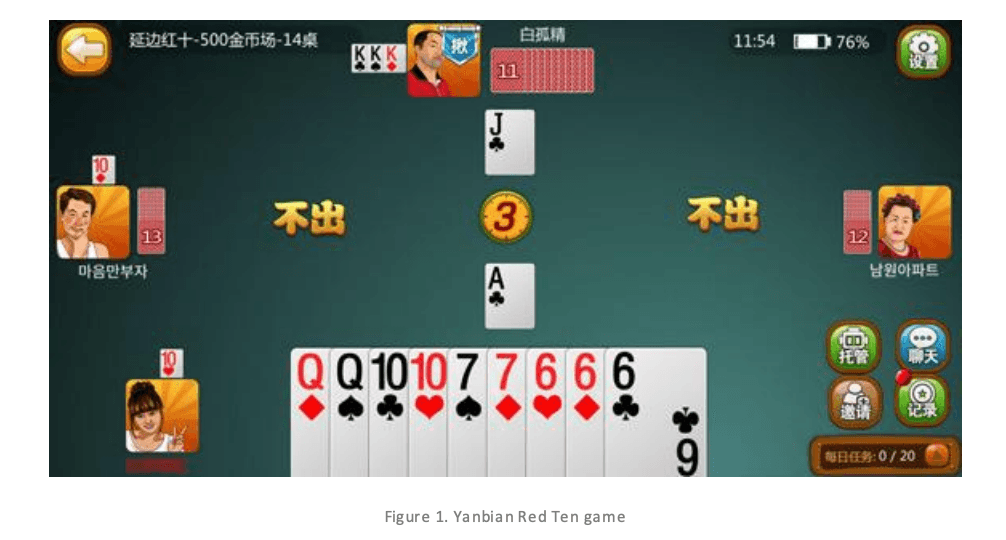
- APT37 embedded the BirdCall backdoor in Android card games distributed by Sqgame.
- BirdCall can capture screenshots, record calls and audio, and exfiltrate contacts, SMS, call logs, media, and private keys.
- Victims typically installed compromised apps via browser downloads; the initial installer was benign but a later update package was malicious.
- ESET found seven Android versions of BirdCall and linked the campaign to a supply-chain compromise active since at least November 2024.
- APT37 has operated since 2012 and previously targeted South Korean entities, North Korean defectors, and media; AhnLab first spotted the Windows BirdCall in 2021.
Read More: https://therecord.media/north-korean-hackers-target-ethnic-koreans-in-china